I sometimes come across customers that would like to relay email through their Exchange Sever from external clients and maybe use a different sending address. Here is how I configure this.
First, we will create a new receive connector via the Exchange Powershell. To do so, open up the Exchange Management Shell (powershell)
Once this loads, use the following command
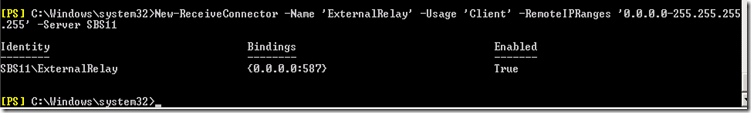
New-ReceiveConnector -Name ‘ExternalRelay’ -Usage ‘Client’ -RemoteIPRanges ‘0.0.0.0-255.255.255.255’ -Server ‘SERVER’
Here is an example:
Now we have created the Receive Connector, and you will see this in the Exchange Management Console.
Let’s check our work, even though it was only one line of text
Now we can verify the network, authentication, and permission groups settings to see how a Client receive connector has been configured. If you go to the properties, you will see that it’s listening on port 587, that it has enabled Basic authentication over TLS, and that it is only allowing Exchange Users (Authenticated Users) to connect. You will see all of this by looking at the connector in the Exchange Management Console.
NOTE: Make sure that port 587 is open in your firewall or this will not work for external users
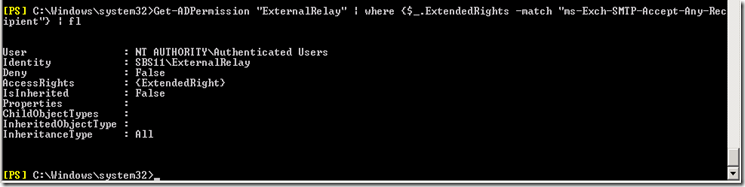
Further inspection of the AD permissions on the receive connector show that authenticated users have the ms-Exch-SMTP-Accept-Any-Recipient right. This is the correct relay permission and you should never have it be owned by anonymous users. You can view and verify this by running the following powershell command:
Get-ADPermission “ExternalRelay” | where {$_.ExtendedRights -match “ms-Exch-SMTP-Accept-Any-Recipient”} | fl
You will see the output looking like:
If it says under user “NT AUTHORITY\ANONYMOUS” then you have an open relay. Stop and delete the connector!
Next, we need to set some additional parameters to make this work.
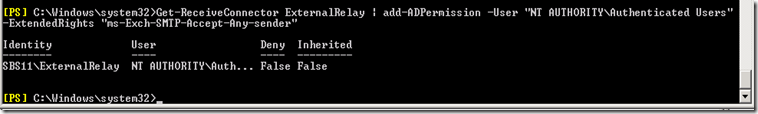
To allow the authenticated user to be able to send email with a different address, we will use the following powershell command
Get-ReceiveConnector ExternalRelay | add-ADPermission -User "NT AUTHORITY\Authenticated Users"-ExtendedRights "ms-Exch-SMTP-Accept-Any-sender"
looking like:
If you are running an SBS 2008 or SBS 2011 server, this also applies:
If you have successfully run the Internet Address Management Wizard from the SBS Console, then your Exchange certificate for TLS has already been installed and configured. You can verify this by running the Get-ExchangeCertificate commandlet and find the certificate with your external DNS domain name. The certificate will have IPWS listed under Services, which stands for IMAP, POP, Web and SMTP respectively.
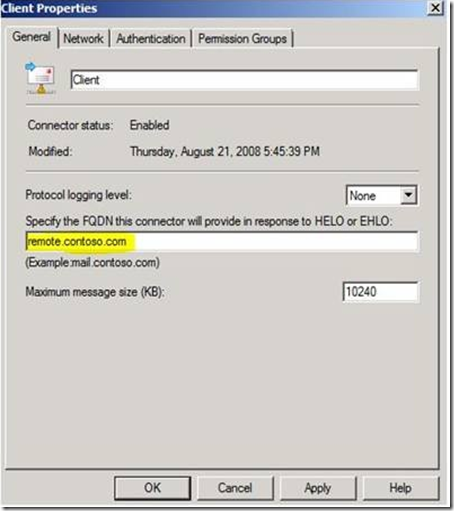
At this point, make sure that your Client receive connector is configured with the same FQDN that is listed in the subject of your Exchange certificate. This will be displayed in the banner:
Once all of this is done, you are ready to setup Outlook, Outlook Express, Windows Mail, etc. Important points here are:
- The client machine must trust both the Exchange certificate and the Root CA in which it was created from. A good test is to open IE on the client and browse OWA to see if you get the certificate warning(s).
- You must configure the mail client to connect on port 587 and to send the proper credentials for authentication.
- The server requires a TLS connection, you must specify this in the mail client
Some of this information in this blog was obtained from the SBS Blog team at http://blogs.technet.com/b/sbs/archive/2008/09/18/how-to-configure-trusted-smtp-relay-in-exchange-on-sbs-2008.aspx


Recent Comments